If a scheduled task invokes a UAC prompt, then the task will fail to run unattended.
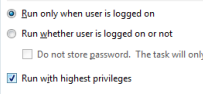
To run a task elevated, select the check box 'Run With Highest Privileges':
The CMD shell, START and RUNAS commands have no built-in options to elevate or run individual commands 'As Admin' (elevated).
When using the Start Menu, hold down Shift+Ctrl when launching an application to launch it 'As Admin' (elevated) this has the same effect as if you right click and select Run as local Administrator.
To run an item on the Start menu / Search /Desktop elevated, select it and then press Ctrl+Shift+Enter on the keyboard.
It is also possible to right click CMD.exe (or its Start menu shortcut) and run a new session 'As Admin'.
Shortcuts can be edited to always run as Admin via Properties ➞ Shortcut ➞ Advanced ➞ then tick ▢ Run as administrator.
To elevate from the command line will require running either VBScript or PowerShell, this does not have to involve completely rewriting existing scripts, you can use a couple of lines of either VBScript or PowerShell to launch an elevated CMD.exe and that will run a batch file elevated.
Another approach is to use a third party utility that will elevate permissions.
When a script is run with elevated permissions several aspects of the user environment will change: The current directory, the current TEMP folder and any mapped drives will be disconnected.
Testing if the current session is elevated can be done with the FSUTIL command (via StackOverflow).
Just paste the following into the top of your batch file:fsutil dirty query %SYSTEMDRIVE% >nul 2>&1 If %errorLevel% NEQ 0 ( Echo Failure, please rerun this script from an elevated command prompt. Exiting... Ping 127.0.0.1 2>&1 > nul Exit /B 1 ) Echo Success: this script is running elevated.An alternative method is to run CACLS agains a protected folder, either method will work on both 32 and 64 bit systems/processes:
"%SYSTEMROOT%\system32\cacls.exe" "%SYSTEMROOT%\system32\config\system" >nul 2>&1 If %errorLevel% NEQ 0 ( Echo Failure, please rerun this script from an elevated command prompt. Exiting... Ping 127.0.0.1 2>&1 > nul Exit /B 1 ) Echo Success: this script is running elevated.To prompt the user to immediately elevate the script and then continue here is a small VBScript that will do that.
In some cases you may wish to run an application without elevation, this will restrict what the application can do.
The undocumented environment variable __COMPAT_LAYER can be used to lower the ExecutionLevel to RunAsInvoker
@Echo Off
SETLOCAL
Set __COMPAT_LAYER=RunAsInvoker
regedit.exeThe example above will run REGEDIT using the user’s native permissions, attempting to modify any protected area of the registry (such as HKLM) within this session will produce an error. Without this, by default Regedit will run elevated.
When a script is elevated, it runs in a new elevated session and the script current directory will default to \Windows\System32\
When writing a script that will be elevated, either hard code the path to any files that you reference, or use pushd "%~dp0" at the start of the script to set the current directory to the location of the .ps1 script.
If a scheduled task invokes a UAC prompt, then the task will fail to run unattended.
To run a task elevated, select the check box 'Run With Highest Privileges':
“A man in public life expects to be sneered at – it is the fault of his elevated situation, and not of himself” ~ Charles Dickens
How-to: Compatibility - Backwards compatibility - runas admin / color - this can also force elevation.
ShellRunAs - Run a command under a different user account (SysInternals).
PowerShell: Run with Elevated Permissions
VBScript: Run with Elevated Permissions
SS64 Forum thread on UAC detection.
Why can’t I bypass the UAC prompt? - Aaron Margosis.
Technet Elevation blog (2010)
elevate - Command-Line UAC Elevation Utility.